When you work with iframes, you quickly realize that the sandbox attribute can either protect your application or completely block important functionality. Understanding how to remove sandbox attributes on the iframe tag is essential if you want full control over embedded content. Many developers struggle with this because the sandbox behaves differently across browsers and security policies.
This guide walks you through everything you need to know, from basic concepts to advanced fixes, so you can confidently manage iframe behavior without breaking your application or exposing it to unnecessary risks.
What The Sandbox Attribute Does In An Iframe
The sandbox attribute is a security feature that restricts what content inside an iframe can do, making it safer but also more limited. By default, it blocks scripts, form submissions, and even navigation, which can cause confusion when your iframe suddenly stops working as expected.
When you are editing HTML or debugging iframe issues, using a reliable tool like free online text editor helps you clearly view and modify attributes without formatting issues, ensuring you do not accidentally break syntax while testing changes.
The key thing you should understand is that sandbox works as a “deny-all, allow-some” system, meaning everything is restricted unless you explicitly allow it with specific values. This design is intentional because it protects users from malicious embedded content, especially in third-party integrations.
Why You May Need To Remove Sandbox Attributes
There are many situations where removing sandbox attributes becomes necessary, especially when your iframe content requires scripts or interaction with the parent page. For example, embedded apps, payment systems, or login widgets often fail if sandbox restrictions are too strict.
You may notice errors or broken functionality, particularly on devices with limited browsers like smart TVs, where sandbox restrictions are enforced more aggressively. In such cases, the issue is not always your code but the environment itself, which limits what can be changed.
However, you should never remove the sandbox blindly because it removes important security protections. Instead, you need to evaluate whether full removal is necessary or if adjusting permissions is a better approach.
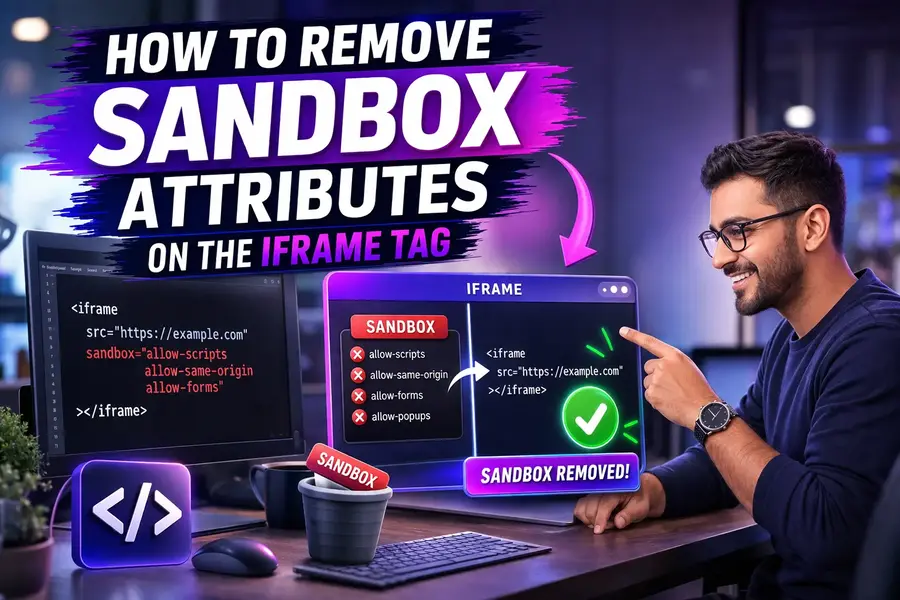
How To Remove Sandbox Attribute Using HTML And JavaScript
Removing the sandbox attribute directly in HTML is straightforward: simply delete it from the iframe tag. However, doing this dynamically with JavaScript requires a deeper understanding of how browsers handle iframe loading.
When working with code snippets or pasted scripts, understanding formatting and cleanup techniques such as edit a paste txt file in a text editor helps you refine your code before applying changes, ensuring your iframe logic remains clean and functional.
If you use JavaScript, the correct approach is to call iframe.removeAttribute(“sandbox”), but this only applies to future loads, meaning the iframe must be reloaded for the change to take effect. This is one of the most misunderstood aspects of iframe behavior, and ignoring it often leads to confusion.
When You Should Modify Instead Of Remove Sandbox
In many cases, completely removing the sandbox attribute is not the best solution, as it exposes your application to unnecessary risks. Instead, you can selectively allow features using sandbox values like allow-scripts or allow-forms.
If you are trying to understand how different tools and environments handle text and code structures, reading about what is a text editor gives you a clearer perspective on how code editing impacts debugging and testing workflows.
This selective approach allows you to maintain security while still enabling required functionality, making your application both safe and flexible. It is especially useful in production environments where user data and interactions must remain protected.
Common Errors When Removing Sandbox Attribute
One of the most common mistakes is expecting the sandbox removal to affect already loaded content, which does not happen. The browser treats the iframe as a separate context, so changes only apply after a reload or navigation event.
Another frequent issue is combining allow-scripts and allow-same-origin, which can unintentionally weaken security. In certain cases, this combination allows the iframe to remove its own sandbox, which defeats the purpose of using it in the first place.
You should also be careful with cross-origin content, as removing sandbox does not bypass browser security policies like CORS. These restrictions still apply and can block interactions between the iframe and the parent page.
Security Risks You Must Consider
Removing sandbox attributes can expose your application to serious risks, including cross-site scripting and unauthorized data access. According to web security studies, over 30% of iframe-related vulnerabilities are linked to improper sandbox configuration.
You need to evaluate whether the embedded content is trusted before removing restrictions. If the content comes from an external source, keeping sandbox enabled with limited permissions is usually the safer choice.
Always follow the principle of least privilege: allow only what is absolutely necessary. This approach minimizes risk while still giving your application the functionality it needs.
Best Practices For Managing Iframe Sandbox
To manage the iframe sandbox effectively, you should always start with full restrictions and gradually allow only the required features. This ensures you maintain control over what the embedded content can do.
You should also test your iframe across multiple devices and browsers, as behavior can vary significantly by environment. Some platforms enforce stricter rules, which may affect how sandbox behaves.
Using clean and structured code improves debugging and reduces errors, especially when dealing with dynamic iframe updates. Consistency in your development workflow makes it easier to identify and fix issues quickly.
Troubleshooting Sandbox Related Issues
If your iframe is not behaving correctly, the first step is to check whether sandbox restrictions are blocking functionality. Browser developer tools can help you identify which permissions are missing.
You should also verify whether the iframe content is same-origin or cross-origin, as this affects what changes you can apply. Understanding this distinction is crucial for effective troubleshooting.
Sometimes the issue is not sandbox itself but how the iframe is embedded or loaded. Reviewing your implementation step by step helps you isolate the root cause and apply the correct fix.
Advanced Tips For Developers
For advanced use cases, you can dynamically create iframes without sandbox and control their behavior through JavaScript. This gives you greater flexibility but requires careful handling to avoid security issues.
You can also reload iframes programmatically after modifying attributes, ensuring changes take effect immediately. This technique is useful in interactive applications where iframe behavior needs to adapt in real time.
Finally, always document your iframe configurations so other developers understand why certain permissions are enabled or disabled. This improves collaboration and prevents future mistakes.
Conclusion
Learning how to remove sandbox attributes on the iframe tag gives you more control over embedded content, but it also comes with responsibility. You must balance functionality and security carefully to avoid exposing your application to unnecessary risks.
By understanding how sandbox works, when to remove it, and when to adjust permissions instead, you can build more reliable and secure web applications. Always test your changes thoroughly and follow best practices to ensure your implementation performs as expected.
FAQs
What does the sandbox attribute do in an iframe?
The sandbox attribute restricts iframe capabilities by disabling scripts, forms, and navigation. It enhances security by isolating embedded content. However, these restrictions can limit functionality, making it necessary to adjust or remove sandbox settings depending on your application needs.
How can you remove the sandbox attribute from an iframe?
You can remove the sandbox attribute by deleting it directly from the iframe HTML tag. In JavaScript, use removeAttribute(“sandbox”) and reload the iframe. This ensures the updated permissions apply to newly loaded content rather than the current session.
Why is removing the sandbox attribute sometimes necessary?
Removing the sandbox attribute becomes necessary when iframe content requires scripts, forms, or interactive features. Many web applications rely on these capabilities, and strict sandboxing can block them. Removing it restores full functionality but should be done cautiously.
Does removing sandbox affect already loaded iframe content?
Removing the sandbox attribute does not affect content already loaded in the iframe. The change only applies after the iframe reloads or navigates to a new page. This behavior often confuses developers expecting immediate changes after removing the attribute.
What are the risks of removing sandbox from an iframe?
Removing sandbox can expose your site to security risks like cross-site scripting or malicious code execution. Without restrictions, embedded content may interact with the parent page. Always ensure the source is trusted before removing sandbox protections entirely.
Can you selectively allow features instead of removing sandbox?
Yes, you can use sandbox values like allow-scripts or allow-forms to enable specific features. This approach maintains security while allowing necessary functionality. It is often better than removing the sandbox completely, especially for third-party or untrusted iframe content.
Why does sandbox removal not work on some devices?
Some devices, such as smart TVs or embedded browsers, enforce strict sandbox policies that cannot be overridden. In these cases, the issue is platform-based rather than code-related. Users may need alternative browsers or environments to bypass such limitations.
How does sandbox affect iframe JavaScript execution?
By default, sandbox blocks JavaScript execution inside the iframe. This prevents scripts from running unless allow-scripts is added. Removing or modifying sandbox allows scripts to execute, enabling dynamic behavior but increasing potential security vulnerabilities if not managed properly.
What is the difference between removing and modifying sandbox?
Removing sandbox eliminates all restrictions, giving the iframe full access to browser capabilities. Modifying sandbox allows specific permissions while keeping others restricted. This selective control is safer and more practical for most applications requiring both functionality and security.
When should you avoid removing sandbox from an iframe?
You should avoid removing sandbox when embedding untrusted or third-party content. Keeping restrictions helps protect users from malicious scripts and data leaks. Instead, enable only necessary permissions to balance functionality with security and maintain a safe browsing environment.